Consistent policy enforcement. complete audit visibility.
UNIFIED GOVERNANCE ACROSS YOUR ENTIRE DATA ESTATE
The Protegrity ESA gives you a centralized and unified point of control over distributed data, ensuring consistent policy enforcement and providing automated audit trails across complex enterprise ecosystems.
Cross-Platform Policy Management
Create, distribute, and apply protections policies for all of your sensitive data across diverse cloud, on-premises, and hybrid systems from a single console.
Compliance Readiness
Streamline audit-readiness for compliance with GDPR, HIPAA, PCI DSS, and other regulations. Automatically generate reports and access detailed, real-time logs to demonstrate regulatory alignment and technical controls.
Access Governance
Control precisely who can access sensitive data—and under what conditions. Consistently apply fine-grained, field-level data access policies based on user role, session context, application domain, or other criteria.
Anomaly-Based Risk Alerts
Proactively surface potential threats before they cause damage. Identify abnormal access behaviors (e.g., excessive attempts, unknown locations) and trigger alerts to security teams or SIEM systems.
Audit-Driven Forensics
Rapidly and thoroughly investigate security incidents and policy violations. Access detailed event logs to see user identity, time, IP, location, and user actions for deep forensic analysis of access attempts.
Centralized Control & Automation Features
THE LATEST
FROM PROTEGRITY
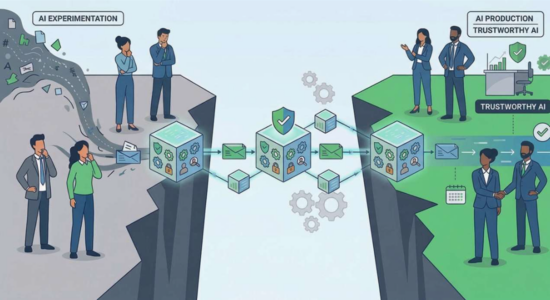
Closing the AI Trust Gap: Why Data-Centric Security Matters
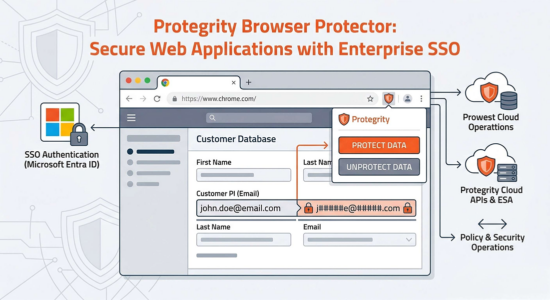
Protegrity Browser Protector: Enterprise Data Protection via Chrome Extension (MV3) with Microsoft Entra ID SSO
Is This Our End? Or Just Another Extinction Event?
MCP Is Gaining Ground, but Governance and Security Still Need Work
A recent AI Business article explores how the Model Context Protocol (MCP) continues to gain traction as an open standard for connecting AI models to tools and data sources, even…
Progress That Sticks: Advancing Women in Tech Through Systems and Accountability — Protegrity Perspective
International Women’s Day is a moment to celebrate progress—but also to be honest about what still hasn’t changed. VMblog’s International Women’s Day 2026 roundup brings together perspectives from leaders across…
Shadow Repositories in Chat Apps: How Discord Can Leak Sensitive Context
For many teams, Discord has become the quickest place to collaborate—especially for developer communities and support. The problem is that speed can also turn chat history into a “shadow repository”…
ENTERPRISE DATA SECURITY
IN A SINGLE PLATFORM
Discovery
Identify sensitive data (PII, PHI, PCI, IP) across structured and unstructured sources using ML and rule-based classification.
Learn moreGovernance
Define and manage access and protection policies based on role, region, or data type—centrally enforced and audited across systems.
Learn MoreProtection
Apply field-level protection methods—like tokenization, encryption, or masking—through enforcement points such as native integrations, proxies, or SDKs.
Learn morePrivacy
Support analytics and AI by removing or transforming identifiers using anonymization, pseudonymization, or synthetic data generation—balancing privacy with utility.
Learn more