A Practical, Browser-Level Approach to Enterprise Data Protection
Most enterprises protect sensitive data at rest and in transit. Data protection techniques such as tokenization, encryption, and masking are widely accepted best practices. They reduce breach impact, limit exposure, and support compliance initiatives across industries.
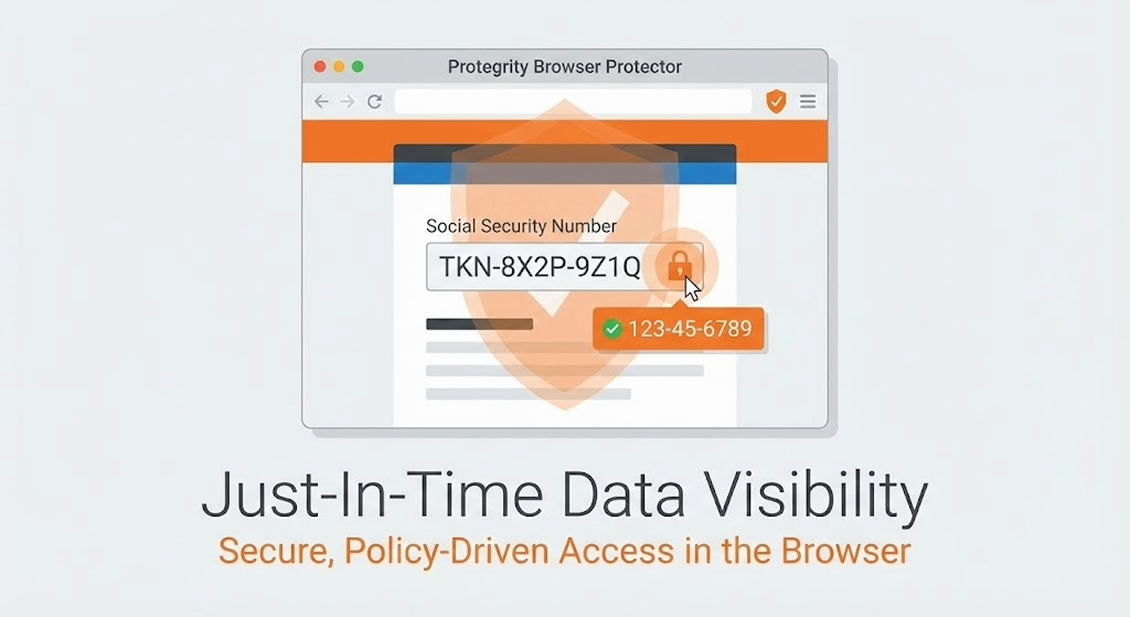
But the moment users need to interact with protected data, security controls begin to create friction within existing workflows. For example, an organization may tokenize Social Security Numbers in storage. But when a call center agent needs to verify a customer, the workflow often requires access to the original value. This is just one instance of how enterprises consistently struggle to use protected data inside web-based applications, where most sensitive data is now consumed.
Protegrity Browser Protector was built to close that gap. It extends Protegrity’s policy-driven data protection to the browser, enabling secure, auditable use of protected data at the moment of consumption—without requiring application code changes or expanding backend access.
The Real Barrier to Data Protection Adoption
Most organizations already protect sensitive data at rest and in transit. The friction appears when humans need to interact with that data inside web applications, whether in internal tools, partner portals, or third-party platforms.
The roadblocks to deploying data protection broadly are familiar:
- Each application needs custom logic to handle protected data.
- Security teams grant broad backend access to avoid blocking users.
- Developers are pulled into security enablement work
- Release cycles and governance slow adoption
As a result, strong data protection remains limited to a subset of systems, even when compliance and security want it applied broadly.
Why the Browser Is the Right Control Point
Modern workflows happen in the browser. Applications render data in the browser. Users act on it there. That is where protected data is either revealed—or remains protected.
Protegrity’s Browser Protector approaches this differently:
- Data remains protected by default
- Users can unprotect data with a right click when authorized
- Enforcement happens at the moment of use in the browser, without requiring application-level code changes.
- Policies are defined and governed centrally through Protegrity Enterprise Security Administrator (ESA).
This aligns with zero trust principles and least privilege access models by shifting control from application code to centrally governed policy.
What Is Protegrity Browser Protector?
Browser Protector is a centrally managed browser extension that allows authorized users to securely reveal protected data within webbased applications. Key characteristics:
- No application changes required
- No sensitive cryptography or keys stored in the browser
- Identityaware access through enterprise SSO
- Centralized, policydriven enforcement using Protegrity
The browser becomes a part of policy enforcement surface—not a security concern.
How Customers Use Browser Protector
Protect Data Without Modifying Applications
Organizations often protect sensitive data upstream so core systems operate only on protected values. But when new applications are introduced—such as analytics tools or eligibility engines—they receive protected data without a built-in way to use it. Enabling unprotect typically requires development work, change control, and security review. Until then, users switch systems, request broader access, or rely on workarounds that increase risk.
- Single-click reveal for individual values when needed, so an online banking call center agent can temporarily reveal a protected SSN to verify end user’s identify without requiring all values to be displayed in unprotected form.
- Column-level unprotect for tabular data, such as lists and reports, so a fraud analyst can view multiple transactions with one click to reconcile records efficiently while keeping the rest of the data fields protected.
- Toggle reveal for cross-application lookup, so a support or business user can briefly make the identifier searchable to find the right record in the next system, complete the task, and immediately return it to protected view.
Enforce Least Privilege Human Access
Instead of granting broad backend permissions:
- Users authenticate through enterprise identity
- Policies define which data elements a user may access
- Access is contextual, temporary, and fully auditable
Accelerate Rollouts Without App Releases
Traditionally, enabling use of protected data requires code changes and formal change control reviews that add time, coordination and process overhead to meet compliance requirements. With Browser Protector:
- Configurations change, not applications
- No new binaries are added to application stacks
- Coverage expands without repeated change control
Security by Design
Browser Protector follows a strict design principle: The browser is not treated as a trusted cryptographic boundary. No keys are stored. No decryption logic runs locally. All sensitive operations remain centrally governed.
What’s Ahead
Protegrity Browser Protector is available for Google Chrome browsers today. Support for additional enterprise browsers, including Microsoft Edge, will follow soon to extend coverage with the same policy model.
The Bigger Shift
Browser Protector reflects a broader shift in enterprise security architecture:
- Policy over code
- Identity over implicit trust
- Access at the moment of use over static exposure
That is how enterprise data protection and tokenization scale across modern workflows, from isolated projects to a default enterprise operating model. To bring justintime data visibility to your browser workflows, learn more about Protegrity Browser Protector.