Cloud Migrations Don’t Need to Wait On Security
Cloud transformation in financial services is no longer a matter of if—but how fast. Yet, too often, security is treated as a blocker to progress.
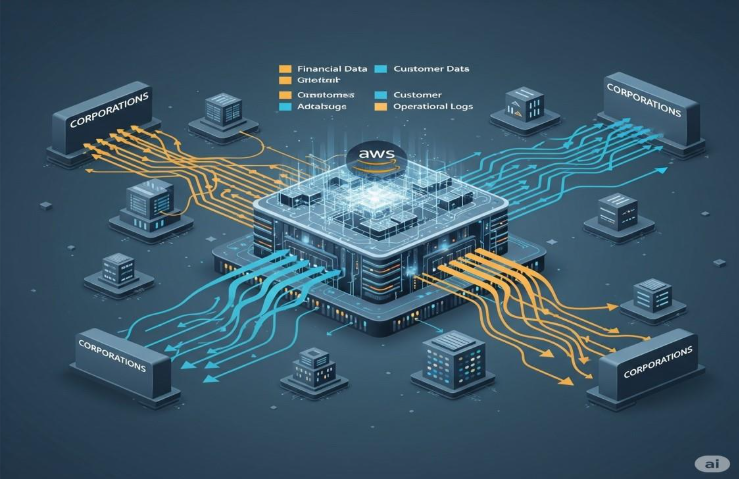
In our recent webinar with AWS, we explored what it really takes for financial services to migrate to the cloud with confidence. The answer wasn’t a surprise, but it was a wake-up call: security must move with your data. Not just at the perimeter or inside isolated systems—but across every database, every application, and every cloud environment.
“Security is job one, but should never be the reason a cloud initiative fails-it should be the reason it succeeds. With the right controls in place, institutions can move faster, reduce risk, and unlock new value.”
— Doug Laroche, Principal Partner Solutions Architect, AWS
For years, security has carried the reputation of being the department of “no”—the gatekeeper, the obstacle to speed, innovation, and change. But that’s not the world financial institutions operate in today. In a landscape defined by agility, AI, and real-time data flows, security isn’t the thing that slows you down—it’s what makes forward movement possible.
Protegrity brings a data-centric model to this equation. Rather than bolt-on solutions or fragmented tools, we enable protection that stays with the data wherever it travels—be it Amazon S3, Redshift, RDS, or beyond. Because we’re platform-agnostic, our clients maintain full control, whether they’re on AWS, multi-cloud, or hybrid infrastructures. And because our tokenization is vaultless, data retains its usability while remaining unintelligible to attackers or unauthorized users.
This is especially critical as AI becomes an embedded part of financial services. While AI was not the central theme of the session, both AWS and Protegrity acknowledged its growing influence—especially in areas like fraud detection, onboarding, risk analysis, and personalized customer experiences. But as Doug emphasized, AI doesn’t erase security concerns; it heightens them. And as Iwona Resia shared, tokenization allows institutions to protect sensitive data even as it flows through large language models or advanced analytics engines. Without that foundation, organizations risk empowering their AI at the cost of their compliance.
One of the most practical insights from the webinar came from examining how financial institutions are actually implementing protection. For some, it’s about securing data on-prem before anything moves. For others, it’s embedding tokenization directly into ETL and streaming workflows. And for many, especially those dealing with inherited cloud environments, protection is applied post-migration—right where the data resides. There’s no one right way—but there is one wrong way: treating security as an afterthought.
The key takeaway from this session was clear: security isn’t a blocker to cloud migration—it’s the unlock. It’s what allows institutions to move quickly, innovate boldly, and operate with trust. When done right, security doesn’t slow the business down. It powers it forward.
If you missed the full discussion, we invite you to watch the webinar replay. Because in today’s environment, the institutions that lead won’t be the ones who wait—they’ll be the ones who secure and scale at the same time.