Protegrity & Oracle
See It In Action
View DemoProtegrity Native
Built and supported by Protegrity, this integration applies field-level protection directly inside Oracle Database—so high-volume workloads stay fast, compliant, and predictable.
Integration type
- Database
Partner
Yes
overview
Protegrity delivers high‑performance data protection by integrating directly with the Oracle kernel through optimized external procedures and shared memory (SGA) access. Whether deployed on single instances, Real Application Clusters (RAC), or Exadata, the solution runs inside the database transaction boundary to remove network latency entirely.
This allows mission‑critical OLTP systems and high‑volume batch workloads to stay fast, compliant, and predictable—while security scales automatically with your Oracle infrastructure.
Key Integration Feature
High‑throughput Oracle environments force a trade‑off: protect sensitive data or preserve performance. Protegrity eliminates that compromise.
By integrating deeply with Oracle Database, Protegrity secures data without slowing transactions, breaking applications, or adding architectural complexity. Protection logic executes inside the Oracle kernel using optimized external procedures that communicate directly with the System Global Area (SGA). The result is microsecond‑level protection that keeps pace with demanding OLTP workloads, RAC clusters, and Exadata systems—without introducing network hops, proxies, or latency.
Features & Capabilities
Explore how Protegrity protects sensitive data inside Oracle—preserving performance, schema compatibility, and policy control across transactional, analytical, and replicated workloads.
01
Vaultless Tokenization: Protect data without breaking Oracle schemas
Why it Matters
Sensitive data is replaced with format‑preserving tokens that fully respect Oracle schema constraints. This protects data without breaking legacy applications, PL/SQL logic, or downstream systems—even when strict data formats are required.
How it Works
A global bank tokenizes account numbers in its core Oracle systems. Because tokens retain valid structure, fraud models running in Oracle Advanced Analytics continue to work unchanged, while raw account numbers never appear in clear text.
02
Shared-Memory Protection: Secure Oracle at microsecond speed
Why it Matters
Standard API‑based or proxy solutions introduce latency and instability. Protegrity runs inside Oracle memory, delivering microsecond‑level performance even under extreme transaction volumes on Exadata and RAC.
How it Works
A telecom provider secures millions of call detail records per second as data moves through Oracle GoldenGate. Protection happens in memory, ensuring data is encrypted before it ever lands in the target system.
03
Dynamic Role-Based Access: Enforce visibility by user and context
Why it Matters
DBAs and privileged users should not automatically see sensitive business data. Protegrity enforces identity‑aware access at query time, without creating or managing duplicate views.
How it Works
In a shared HR database, a Payroll_Admin sees clear‑text salary data, while a System_DBA running the same query sees masked values. Administrative access no longer equals data access.
04
Native SQL & PL/SQL Integration: Protect data inside existing workflows
Why it Matters
Security should not slow developers down. Protegrity integrates directly into existing SQL and PL/SQL workflows, with no key management or external libraries required.
How it Works
Developers call a Protegrity function inside an insert statement. Policies are enforced instantly, ensuring no clear text is written to disk or redo logs—without changing application logic.
05
Centralized Policy Federation: Define once, enforce across Oracle estates
Why it Matters
Managing data protection policy database‑by‑database doesn’t scale. Protegrity lets you define policies once and enforce them everywhere, eliminating drift and manual updates.
How it Works
A security team updates a masking rule in the Enterprise Security Administrator (ESA). The change takes effect immediately across Oracle E‑Business Suite, OLTP systems, and data warehouses, with no restarts or redeployments.
Architecture &
Sample Data Flow
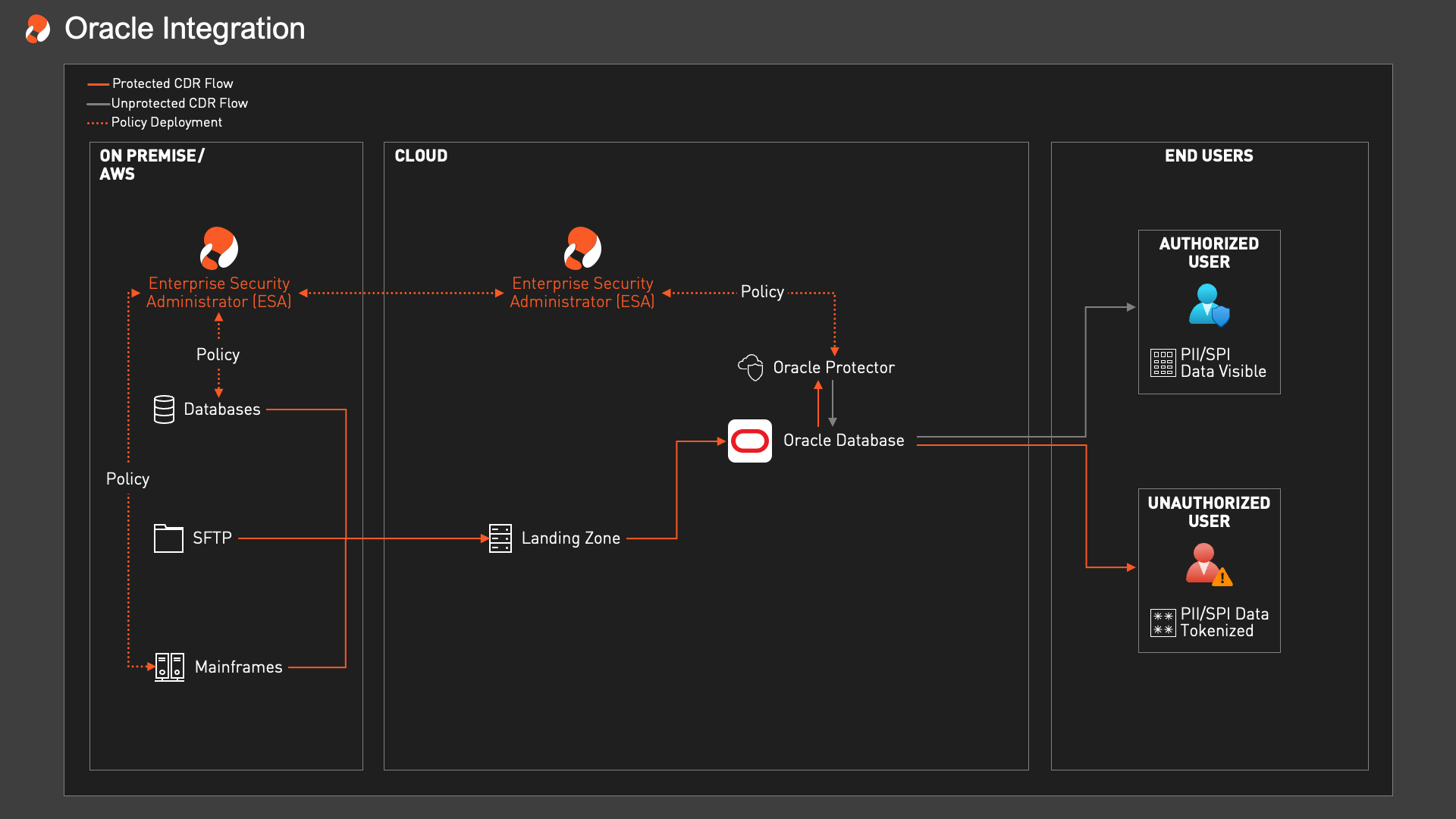
Protegrity’s architecture is purpose‑built for high‑performance Oracle environments. By attaching directly to the Oracle Database kernel and leveraging shared memory (SGA), Protegrity creates a persistent security layer that operates inside the transaction itself. This design ensures consistent protection across single‑instance databases, RAC clusters, and Exadata platforms, without changing how data is accessed, processed, or analyzed.
The data journey
Visualizing the data journey
The data journey
The data journey explained
-
01
High-speed ingestion
Sensitive fields can be protected as data enters Oracle through SQL*Loader, Data Pump, or GoldenGate. Protegrity applies tokenization, encryption, or masking inline so bulk loads and replication pipelines stay secure without adding network latency.
-
02
Transactional protection inside Oracle
Within Oracle Database, Protegrity can be invoked directly from SQL and PL/SQL during inserts, updates, and queries. Protection runs inside the transaction boundary, helping OLTP, RAC, and Exadata environments secure sensitive values while preserving performance and schema integrity.
-
03
Controlled data access at query time
Authorized users and systems can unprotect values through SQL views, stored procedures, or policy-aware functions at query time. Access is enforced dynamically based on role and context, so users only see the level of data they are permitted to use.
-
04
Governed delivery to analytics and apps
Protected Oracle data can flow safely into downstream tools such as Oracle Analytics Cloud, Tableau, and JDBC/ODBC-connected applications. Teams can analyze and operationalize governed data while limiting clear-text exposure to approved users and use cases.
Use Cases
See how organizations use Protegrity + Oracle to protect sensitive data in high-performance database environments—so teams can support analytics, compliance, and operational workloads without exposing raw values.
Finance
Protecting high-volume transactions and customer data in Oracle
Challenge
A global Tier-1 bank needed to secure millions of daily credit card transactions and customer records in Oracle Exadata while meeting PCI DSS and GDPR requirements. The challenge was to protect sensitive values without adding latency that could disrupt payment processing, fraud detection, or other real-time workloads.
Solution
Protegrity applied vaultless tokenization and role-aware protection directly inside Oracle using native integration with shared memory and Oracle-aware policy enforcement. The bank preserved schema integrity, maintained throughput across Exadata and RAC environments, and enforced different levels of visibility based on role, process, and use case.
Result
The bank reduced compliance reporting effort, maintained PCI-aligned controls, and enabled fraud and analytics teams to work on protected data without exposing raw account values. Oracle performance remained stable even in high-frequency transaction environments.
Healthcare Payers
Protecting PHI in Oracle for claims, care, and analytics
Challenge
A healthcare payer needed to secure member, claims, and provider data stored in Oracle while supporting downstream reporting, care operations, and analytics. The organization had to protect PHI and other regulated identifiers without slowing claims processing or creating separate data pipelines for different user groups.
Solution
Protegrity enforced tokenization, masking, and role-based unprotection directly inside Oracle so sensitive values could remain protected at rest and during query execution. Policies were centrally managed and applied consistently across operational systems, reporting environments, and authorized downstream applications.
Result
The payer improved control over PHI exposure, simplified audit readiness, and enabled analysts and operational teams to work with governed data without duplicating databases or exposing clear text more broadly than necessary.
DEPLOYMENT
Deploy Protegrity in Oracle the way enterprise teams actually run Oracle—inside transactional databases, clustered environments, and high-throughput replication pipelines. Protection stays close to the data, while policies are managed centrally for consistent enforcement.
Native Oracle Database integration
RAC and Exadata environments
Bulk load and replication workflows
Role-aware access at query time
Centralized policy management
RESOURCES
Guides and technical references to help your team deploy, operate, and scale Protegrity with Oracle. From native database integration and PL/SQL patterns, to policy administration and governed data access.
Docs Center
Explore setup guidance, API and function references, policy configuration, and implementation patterns for protecting sensitive data in Oracle environments.
READ MOREESA Oracle Configuration Guide
Learn how to configure Oracle in Protegrity ESA for database-backed member sources, role management, and policy-driven access controls.
READ MOREFrequently
Asked Questions
Here are five common questions related to the integration, deployment, and features of the Oracle and Protegrity solution, with their answers:
Protegrity supports the core Oracle Database platform (including 19c, 21c, and 23ai), Oracle Exadata, and Real Application Clusters (RAC). Beyond the database engine, we support high-speed data movement and replication utilities like Oracle GoldenGate, Data Pump, and SQL*Loader. The integration is architected around optimized external procedures that communicate directly with the System Global Area (SGA), allowing any SQL transaction, PL/SQL trigger, or report to leverage high-speed protection without network latency.
Protegrity fully supports Oracle’s hybrid nature, covering on-premise appliances (Exadata), Oracle Cloud Infrastructure (OCI), and Oracle databases running on AWS, Azure, or Google Cloud. You can deploy the protection policy centrally and enforce it consistently whether your database sits in your private data center or is managed via Exadata Cloud@Customer. For data exported from Oracle to other systems (e.g., a Kafka stream or Snowflake), the same centralized policies ensure data remains secure and interoperable.
Protegrity supports vaultless tokenization, encryption, masking, hashing, and format-preserving encryption, all centrally managed via the Enterprise Security Administrator (ESA). This centralized approach ensures that policies (e.g., “Mask Credit Card for Support Staff”) are defined once and pushed to all Oracle instances simultaneously. Policy updates, key rotation, and separation of duties are handled automatically by the ESA, ensuring that DBAs manage the infrastructure while security officers manage the access rules.
Our customers benefit from:
- Seamless RAC Integration: Run secure transactions on protected data using shared-memory processes that distribute load across all RAC nodes.
- Exadata Scalability: Performance scales automatically with your infrastructure; as you add compute nodes to your Exadata rack, protection throughput increases without additional configuration.
- Secure Oracle Analytics: Enable safe use of Oracle Analytics Cloud and in-database machine learning by sanitizing sensitive fields before they are processed by models or dashboards.
- Consistent Governance: Uniform protection logic applied identically across production OLTP systems, data warehouses, and disaster recovery sites.
Protegrity integrates with Oracle via optimized External Procedures (ExtProc) and shared libraries that attach directly to the database memory space (SGA). This allows users to query data or execute transactions using standard SQL or PL/SQL stored procedures while Protegrity handles the cryptographic operations in the background. Unlike external API calls or proxy appliances, these internal integrations incur near-zero latency, preserving the performance of mission-critical applications.
See the
Protegrity
platform
in action
Accelerate data access and turn data security into a competitive advantage with Protegrity’s uniquely data-centric approach to data protection.
Get an online or custom live demo.