Protegrity & Teradata
See It In Action
View DemoProtegrity Native
Built and supported by Protegrity, this integration applies field-level protection directly inside Teradata Vantage—so high-volume warehouse workloads stay fast, governed, and compliant.
Integration type
- Data Warehouse
Partner
Yes
Supported platforms
- AWS
- Azure
- GCP
overview
Protegrity delivers data protection that behaves like a built‑in capability of Teradata Vantage, not a bolt‑on control. The solution runs directly inside the Teradata environment, using local compute and storage resources to protect data without network hops, external services, or API calls. Whether you are ingesting large batch loads, running high‑concurrency BI queries, or executing advanced analytics, Protegrity operates in lockstep with Teradata’s Massively Parallel Processing (MPP) architecture. Security workloads are distributed across the same AMPs that execute your queries—so protection scales automatically as your warehouse scales. The result: enterprise‑grade security, zero added infrastructure, and no performance trade‑offs.
Key Integration Feature
Protegrity’s native integration with Teradata Vantage delivers persistent, data‑centric security across the entire analytics lifecycle—without forcing teams to choose between protection and performance. By leveraging Teradata’s MPP architecture and optimized User Defined Functions (UDFs), sensitive data is protected continuously—from high‑volume ingestion and ELT pipelines to ad‑hoc SQL, dashboards, and machine learning workloads. Protection logic executes in parallel, inside the database engine, eliminating latency and data movement. This allows Teradata customers to fully exploit their data—at production scale—while meeting strict privacy, residency, and compliance requirements.
Features & Capabilities
See how Protegrity protects sensitive data natively inside Teradata Vantage—using in-database functions, centralized policy, and MPP-scale performance for analytics, BI, and AI.
01
Vaultless Tokenization for Analytics-Ready Data
Why it Matters
Replace sensitive data with format‑preserving tokens that retain referential integrity and analytical value inside Teradata Vantage—without the performance penalty of lookup tables or external vaults. Tokens maintain original schemas (length, format, data type), so existing SQL, joins, and applications continue to work without modification.
How it Works
A major retailer stores tokenized customer transaction data in Teradata. Because the tokens pass validation and preserve structure, data science teams can train models in ClearScape Analytics on full production datasets—without exposing real customer identities.
02
MPP-Scale Protection Inside the Database Engine
Why it Matters
Security scales linearly with your warehouse. By executing protection logic through optimized UDFs on Teradata AMPs, Protegrity eliminates data movement and network latency during ingestion, transformation, and query execution—even at massive scale.
How it Works
A healthcare analytics firm processes nightly patient data using FastLoad. Protegrity’s embedded UDFs execute protection in parallel across all nodes, reducing encryption windows from hours to minutes—while keeping all data inside the database kernel.
03
User-Aware Policy Enforcement at Query Time
Why it Matters
Enforce least-privilege access dynamically without duplicating data or maintaining complex view hierarchies. Protegrity resolves the active Teradata user or role at query time and automatically determines whether data should appear in clear text, masked, or tokenized.
How it Works
A single employee dataset safely serves multiple teams. A regional manager querying the view sees clear names and salaries, while a data scientist sees tokenized identifiers and masked compensation ranges—driven entirely by policy.
04
Native SQL Integration Without External Calls
Why it Matters
Protect data directly in SQL without embedding APIs, secrets, or credentials into ETL jobs, stored procedures, or BI tools. This reduces operational risk, simplifies development, and accelerates adoption.
How it Works
Data engineers call standard SQL functions such as
Protect_SSN(column), while Protegrity UDFs handle cryptography and policy enforcement locally on each node—preventing sensitive keys from appearing in logs or source code.05
Centralized Policy Federation Across Teradata Environments
Why it Matters
Define protection rules once and enforce them everywhere. Policies are managed centrally in Protegrity Enterprise Security Administrator (ESA) and pushed directly into Teradata—eliminating manual updates and configuration drift.
How it Works
A financial institution defines a global SSN policy in ESA. The rule is instantly enforced across all mapped Teradata columns, ensuring users without the “Compliance‑Officer” role receive masked data—regardless of tool or query path.
Architecture &
Sample Data Flow
Protegrity integrates directly into Teradata’s MPP core using optimized User Defined Functions (UDFs) deployed on database nodes. This creates a pervasive, in‑database security layer that operates inside the SQL engine itself. Protection policies apply consistently across standard SQL queries, bulk ingestion utilities, and advanced analytics in ClearScape Analytics—ensuring sensitive data remains protected throughout its lifecycle.
The data journey
Visualizing the data journey
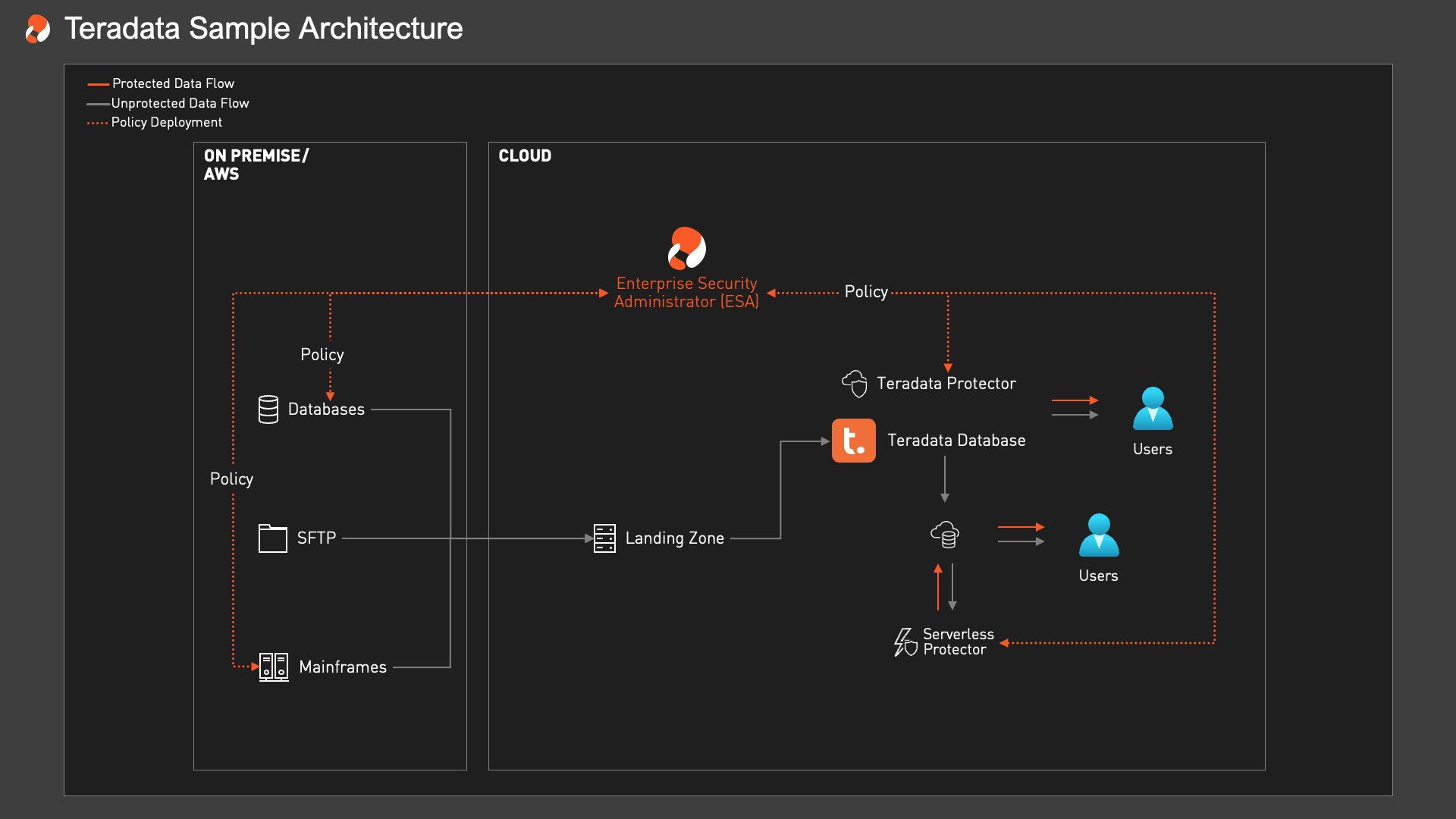
The data journey
The data journey explained
-
01
Data ingestion
Sensitive data can be protected as it enters Teradata Vantage through high-speed ingestion paths such as TPT, FastLoad, or upstream ETL pipelines. Protegrity applies tokenization or encryption before data is broadly consumed, helping ensure raw PII, PHI, and PCI data does not land unprotected in analytic tables.
-
02
Data transformation
As teams run ELT, SQL transformations, joins, and aggregations inside Teradata, Protegrity UDFs execute locally across AMPs in parallel. Protection stays inside the database engine, preserving schema compatibility, referential integrity, and warehouse performance at scale.
-
03
Governed data access
Business users, BI dashboards, and ClearScape Analytics workloads can operate on protected data by default. At query time, Protegrity enforces policy based on user role and context—determining whether data is shown in clear text, masked, or tokenized without duplicating tables or maintaining separate views.
-
04
Controlled unprotection and auditability
When approved workflows require access to original values, Protegrity enables controlled unprotection inside Teradata or through authorized downstream tools. Every protection and unprotection event is logged to support audit readiness, compliance reporting, and centralized governance.
Use Cases
See how organizations use Protegrity + Teradata to protect sensitive data inside high-performance warehouse environments—so teams can support analytics, AI, and compliance without exposing raw values or slowing down queries.
Finance
Protecting payment, customer, and transaction data for high-scale analytics in Teradata.
Challenge
A financial institution needed to secure customer and transaction data in Teradata while supporting large-scale reporting, fraud analytics, and regulatory requirements such as PCI-DSS and GDPR. The challenge was to protect sensitive fields without introducing latency, breaking joins, or reducing the utility of the warehouse for analysts and data science teams.
Solution
Protegrity applied vaultless tokenization and policy-based protection directly inside Teradata Vantage using native UDFs. Sensitive fields remained protected in place while preserving schema compatibility, referential integrity, and query performance across BI dashboards, SQL workloads, and advanced analytics.
Result
The organization reduced exposure of PCI and PII data, simplified audit readiness, and enabled teams to analyze governed data at scale without moving it outside Teradata or exposing clear text more broadly than necessary.
Healthcare Payers
Protecting PHI in Teradata for claims, reporting, and advanced analytics.
Challenge
A healthcare organization needed to secure PHI and member data stored in Teradata while supporting reporting, analytics, and operational access for different user groups. The challenge was to enforce HIPAA-aligned protection without slowing complex queries or creating separate datasets for every role.
Solution
Protegrity embedded protection directly inside Teradata using native UDFs and centralized policy federation through ESA. Sensitive data remained protected within the warehouse, while user-aware policies determined whether clinicians, analysts, or administrators saw clear text, masked values, or tokens at query time.
Result
The organization improved control over PHI exposure, maintained analytical usability across the warehouse, and demonstrated that strict governance and warehouse-scale performance could coexist in the same Teradata environment.
DEPLOYMENT
Deploy Protegrity natively inside Teradata Vantage so protection runs where analytics already happen—inside the warehouse, across MPP nodes, and under centralized policy control.
In-database UDF deployment
Query-time enforcement and secure views
Bulk load and ELT integration
Hybrid and cloud deployments
Centralized policy management
RESOURCES
Guides and supporting resources to help your team plan, deploy, and scale Protegrity with Teradata—from native UDF integration and policy management to secure analytics and governed data access.
Customer Case Study
See how enterprises use Protegrity with Teradata to secure sensitive data at warehouse scale while preserving performance for reporting, analytics, and AI workloads.
READ MOREDocs Center
Explore technical guidance, policy administration, and implementation patterns for protecting sensitive data in Teradata environments with native, in-database controls.
READ MOREFrequently
Asked Questions
Here are five common questions related to the integration, deployment, and features of the Teradata and Protegrity solution, with their answers:
Protegrity supports the core Teradata Vantage platform, including the SQL Engine, ClearScape Analytics, and bulk loading utilities like Teradata Parallel Transporter (TPT) and FastLoad. The integration is architected around native User Defined Functions (UDFs) that run directly on the database nodes, allowing any SQL-based query, report, or analytical model to leverage high-speed protection without data movement.
Protegrity fully supports Teradata Everywhere, covering on-premise appliances (IntelliFlex), public cloud deployments (Vantage on AWS/Azure/Google Cloud), and VMware environments. You can deploy the protection policy centrally and enforce it consistently whether your data warehouse sits in your private data center or the public cloud. For data exported from Teradata to other systems (e.g., a Hadoop data lake or Kafka stream), the same centralized policies ensure data remains secure and interoperable.
Protegrity supports vaultless tokenization, encryption, masking, hashing, and format-preserving encryption, all centrally managed via the Enterprise Security Administrator (ESA). This centralized approach ensures that policies (e.g., “Mask SSN for Analysts”) are defined once and pushed to all Teradata nodes simultaneously. Policy updates, key rotation, and separation of duties are handled automatically by the ESA, ensuring that database administrators manage infrastructure while security officers manage access rules.
Our customers benefit from:
- Seamless MPP Integration: Run secure SQL analytics on protected data using native UDFs that execute in parallel across all AMPs.
- Linear Scalability: Performance scales automatically with your Teradata system; as you add nodes, protection throughput increases without additional configuration.
- Secure Advanced Analytics: Enable safe use of ClearScape Analytics and in-database modeling by sanitizing sensitive fields before they are processed by machine learning algorithms.
- Consistent Governance: Uniform protection logic applied identically across production, test, and disaster recovery environments.
Protegrity integrates with Vantage via optimized C/C++ User Defined Functions (UDFs) that are installed directly into the database kernel. This allows users to query data or train models using standard SQL or Python/R (via ClearScape) while Protegrity handles the cryptographic operations locally on the compute nodes. Unlike external API calls, these internal functions incur zero network latency. Please refer to the Integration Features section for more details.
See the
Protegrity
platform
in action
Accelerate data access and turn data security into a competitive advantage with Protegrity’s uniquely data-centric approach to data protection.
Get an online or custom live demo.