Category: Blogs
-

-
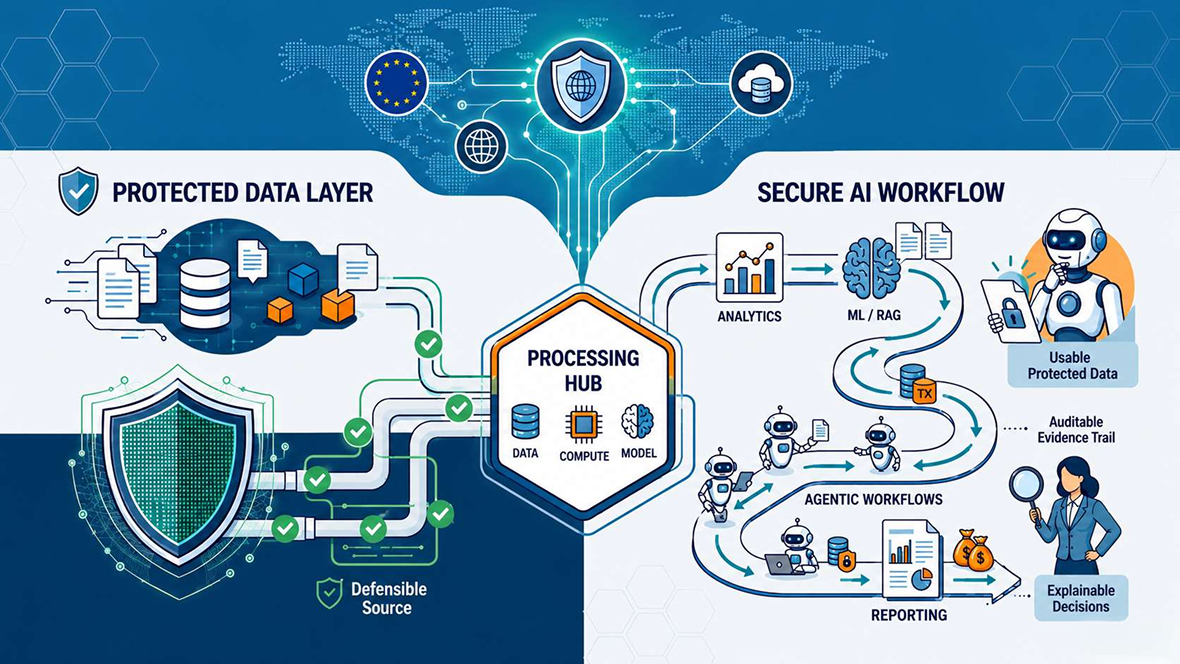
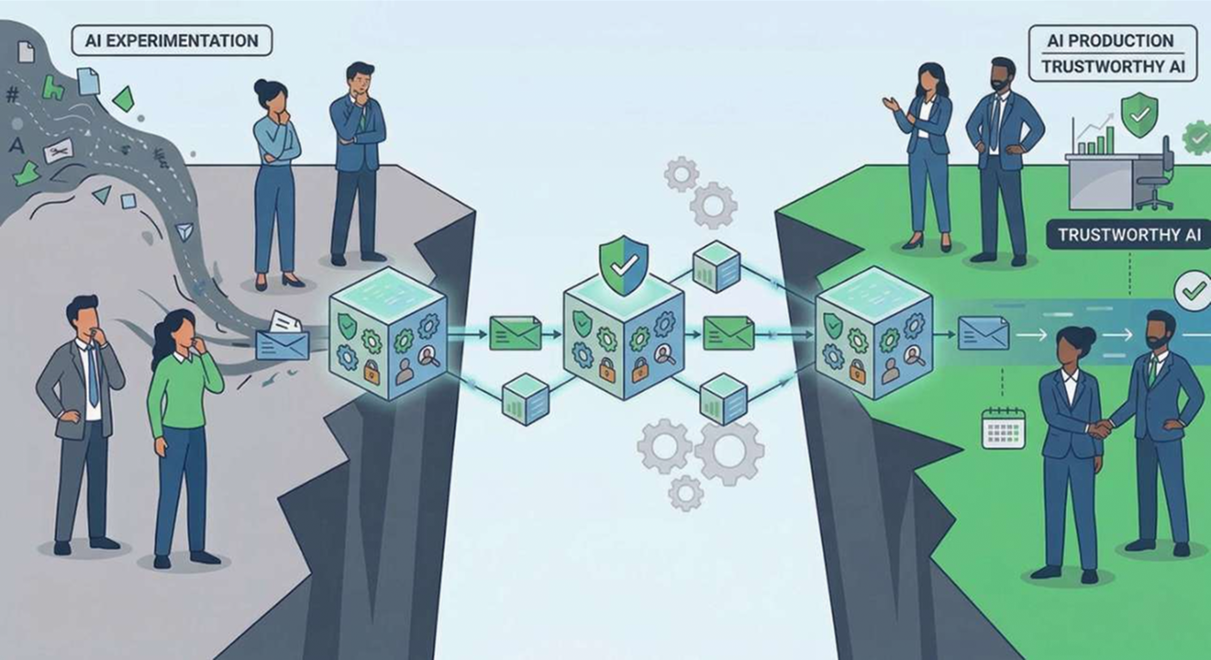
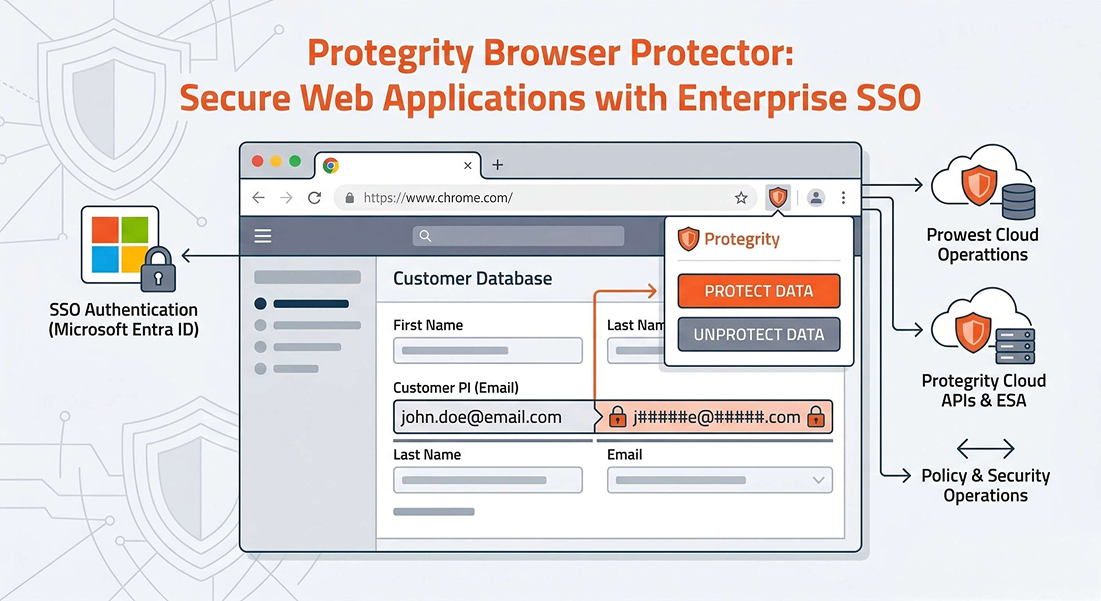
Why Defensible AI Starts at the Data Layer
Defensible AI requires more than accurate outputs. Learn why regulated enterprises need data-layer protection to keep sensitive data usable, governed, and auditable across analytics, RAG, and agentic AI workflows.
-
-
-
-
-
-
-

-