Remove Security Friction From Data Projects.
One platform.
Three editions.
Protegrity
AI Developer Edition
Protegrity
AI Team Edition
Protegrity
AI Enterprise Edition
Built to Protect. Designed to share.
Data Consumption
Data Security
Secure data where it lives, control how it’s used.
Data Sources
Enterprise Data Security
In A Single Platform
the data lifecycle—including for analytics and AI.
Discovery
Identify sensitive data (PII, PHI, PCI, IP) across structured and unstructured sources using ML and rule-based classification.
Learn moreGovernance
Define and manage access and protection policies based on role, region, or data type—centrally enforced and audited across systems.
Learn moreProtection
Apply field-level protection methods—like tokenization, encryption, or masking—through enforcement points such as native integrations, proxies, or SDKs.
Learn MorePrivacy
Support analytics and AI by removing or transforming identifiers using anonymization, pseudonymization, or synthetic data generation—balancing privacy with utility.
Learn morePROTECTION THAT MATCHES YOUR STACK
One-size-fits-all data protection limits data projects from the start. Protegrity lets you choose data protection tailored to the specific architecture and use case of any data project. — across cloud platforms, applications, databases, mainframes, and files — all managed from a central policy engine.
Protect data in cloud-native platforms like Snowflake, BigQuery, Redshift, and other managed services. These protectors run inside the data platform itself to enforce policy without routing data externally—maintaining performance and compatibility with analytics, AI, and reporting tools.
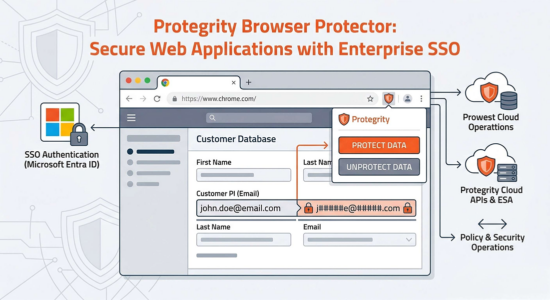
Secure data before it’s shared with third-party SaaS platforms. Apply tokenization, masking, or redaction to outbound data—ensuring privacy is preserved even after data leaves internal control.
Apply protection between applications and data sources using proxies (like DSG) or REST containers. These protectors secure data in motion—without requiring changes to application logic or code.
Enforce field-level protection in databases and data warehouses—whether traditional RDBMS (e.g., Oracle, SQL Server) or modern platforms (e.g., Hive, Synapse). Protection is applied during query execution or data storage, supporting structured policy enforcement without disrupting workflows.
Secure data within legacy infrastructure like mainframes, flat files, and batch processing environments. These protectors work within core systems to enforce policy without requiring data to be offloaded or modernized.
Amplify Native Data Security. Get More Value From Data Platforms.
Protegrity seamlessly integrates with leading data platforms, plugging gaps in native data security tools and giving you smarter data protection — so you can do more with your data and get more out of your investment.



““Protecting our customer’s PII data is essential. Protegrity tokenization accelerates our secure transformation while enabling advanced analytics with protected data.” “
Data-centric security designed for modern data projects
Protegrity simplifies agile data protection by removing limits—covering all your data types, integrating with all your platforms, and freeing you to match our broad range of advanced protection methods to the specific risk and demands of each data project.
Protect the data itself
Secure the data element, not just the system. Control exactly who sees what with field-level tokenization, encryption, or masking, ensuring protection follows the data.
maintain data utility & referential integrity
Keep protected data usable for reports, dashboards, and AI. Format-preserving protection methods let data teams run queries and train models without exposing sensitive information.
ensure continuous compliance
Simplify compliance across complex environments. Centrally create and manage policies, monitor all access, and automate audit logging for consistent enforcement and proof.
Build future-ready data protection
Protect data uniformly wherever it lives—AWS, Azure, Snowflake & more. Centralized control across clouds reduces complexity and ensures consistent security, now and for the future.
Accelerate business-critical data projects
Speed up development cycles with easy integration. Embed protection via lightweight APIs, SDKs, or containers (Docker/K8s), empowering developers to build securely, faster.
POWERING CRUCIAL DATA
PROJECTS. PROTECTING CRITICAL DATA TYPES.
From cloud analytics to GenAI security, see how Protegrity enables business-critical data projects by enabling secure access to vital data.
THE LATEST FROM PROTEGRITY
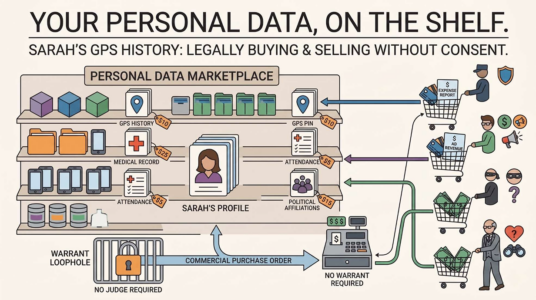
Protegrity on Health App Data Privacy and Consumer Data Protection
A recent U.S. News & World Report article examines the privacy risks tied to consumer health apps, wearables, and health-tracking devices. The piece explores what data these tools may collect,…
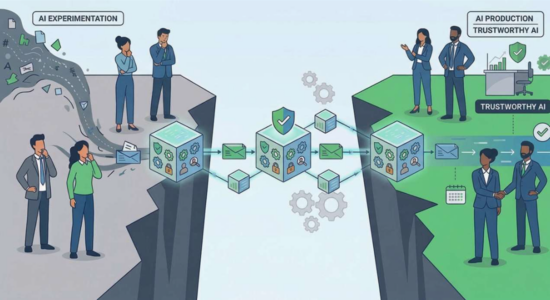
Protegrity on What Trustworthy Healthcare AI Requires | Protegrity
AI is showing up fast across healthcare—both in clinical settings and behind the scenes—but responsible deployment depends on more than performance. In a Healthcare IT Today roundup, industry leaders outline…
Protegrity Expands Team to Advance AI Innovation and Data Protection
New Hires Strengthen AI Capabilities, Product Strategy and Global Impact Menlo Park, CA – Protegrity, taking its global leadership in data protection and privacy into AI Security, today announced new…